
Compare Docker and Podman in 2026: tradeoffs in security, cost, Kubernetes support, and when to use each or a hybrid.
Choosing between Docker and Podman in 2026 boils down to your priorities: cost, security, and workflow compatibility. Docker remains the go-to for ease of use and development, while Podman offers a secure, rootless, and cost-free alternative - ideal for enterprises and regulated industries.
Here’s what you need to know:
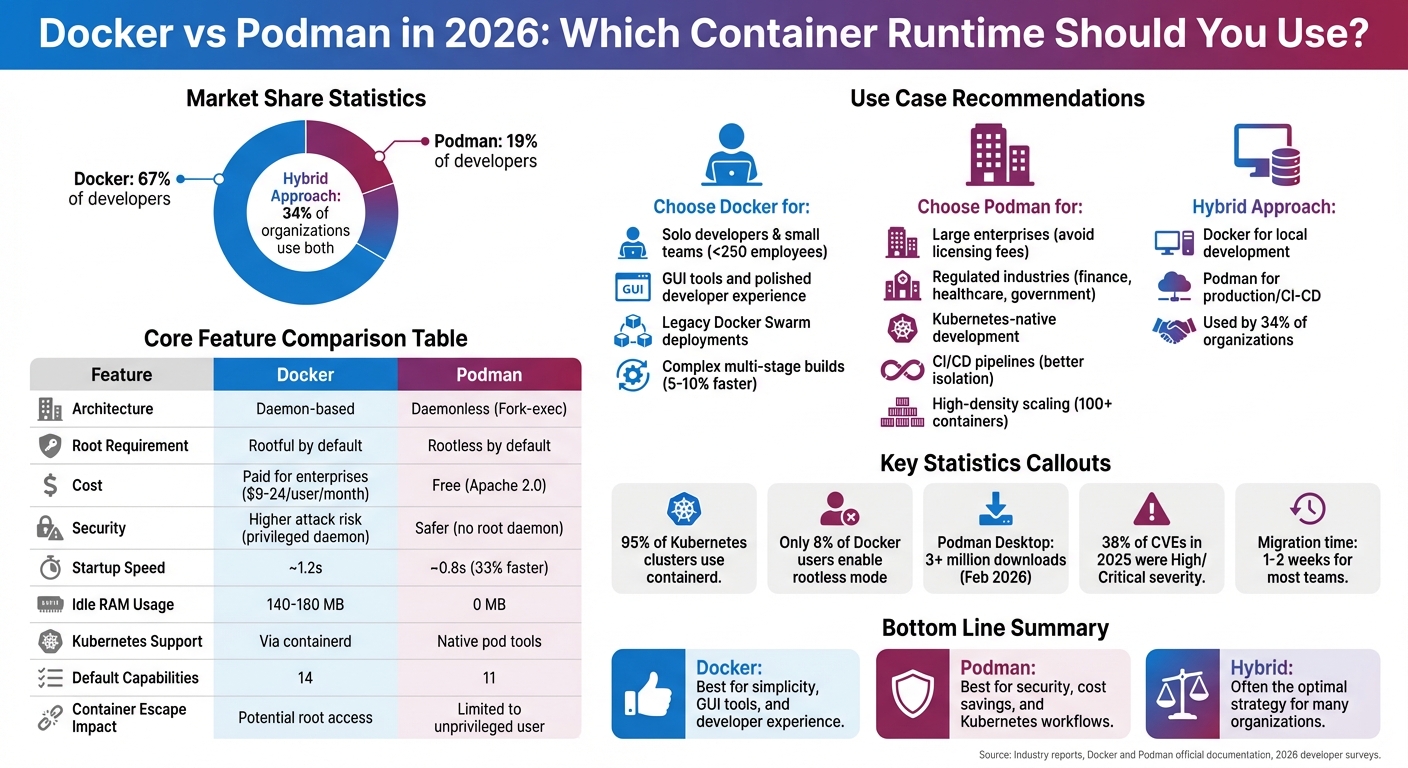
- Docker: Used by 67% of developers, it’s favored for local development, GUI tools, and faster builds but comes with licensing fees for larger teams.
- Podman: Gaining traction (19% market share), it’s daemonless, rootless by default, and free, making it a top choice for CI/CD pipelines and security-conscious teams.
- Hybrid Approach: 34% of organizations use Docker for development and Podman for production or CI workflows.
Quick Comparison:
Feature
Docker
Podman
Architecture
Daemon-based
Daemonless (Fork-exec)
Root Requirement
Rootful by default
Rootless by default
Cost
Paid for enterprises
Free
Security
Higher attack risk
Safer (no root daemon)
Startup Speed
~1.2s
~0.8s
Kubernetes Support
Via containerd
Native pod tools
Bottom Line:
Use Docker for simplicity and GUI tools. Choose Podman for security, cost savings, and Kubernetes-native workflows. For many, a hybrid strategy works best.
Docker vs Podman 2026: Complete Feature Comparison Chart
Podman vs Docker in 2026: What's Really Different?
sbb-itb-bfaad5b
Container Runtimes in 2026: The End of Docker's Dominance
Docker's once-dominant position in containerization has shifted dramatically. Three key developments drove this change: Kubernetes v1.24's removal of dockershim, Docker Desktop's 2021 licensing changes, and the industry's growing focus on zero-trust security architectures. These changes didn’t eliminate Docker but ended its uncontested dominance. The adoption of OCI standards played a major role in speeding up this transformation.
The Open Container Initiative (OCI) introduced standardized image and runtime specifications, breaking Docker's proprietary hold on container formats. This opened the door for other runtimes to flourish. Today, 95% of Kubernetes clusters rely on containerd as their default runtime, while Podman has secured 19% of the developer market. Kubernetes' decision to drop dockershim underscored the industry's move toward streamlined, purpose-built runtimes like containerd and CRI-O.
"The architectural decisions made in Docker's early days - specifically the reliance on a central, root-privileged daemon - have started to show their age." – Toolshelf Team
Security has become a top priority, especially in regulated sectors like finance, healthcare, and government. Docker's reliance on a central daemon with root privileges is increasingly seen as a liability. This setup creates both a single point of failure and a significant attack surface. If dockerd is compromised, attackers could gain root access to the host. Podman, with its daemonless and rootless-by-default design, directly addresses these concerns. It also consumes zero idle RAM, compared to Docker's 140–180 MB daemon footprint. These advantages have made Podman a popular choice for security-conscious teams.
Today, most organizations have adopted a hybrid runtime strategy. Docker remains a favorite for local development due to its ease of use, while Podman is favored for CI/CD pipelines thanks to its security and cost benefits. Meanwhile, containerd is the go-to runtime for production Kubernetes clusters, valued for its lightweight design and compatibility with CNCF tools. This approach, now used by 34% of organizations, acknowledges that no single runtime can meet all needs. The growing integration of Podman into modern development tools further signals its growing acceptance as a first-class option alongside Docker.
Docker Desktop: Features, Pricing, and Licensing Issues
Docker Desktop remains a top choice for container development in 2026. The latest version (Engine 29.2.1, released in February 2026) brings some impressive updates, including containerd as the default image store, BuildKit v0.27 for quicker builds, and experimental support for nftables. Its user-friendly GUI dashboard, Kubernetes integration, and Docker Scout vulnerability scanning continue to make it a standout tool for developers. However, these advancements are overshadowed by ongoing licensing challenges.
The licensing model for Docker Desktop has been a sticking point for enterprises since 2021, and the issues remain unresolved. While individuals and small businesses (fewer than 250 employees and under $10 million in annual revenue) can use it for free, larger organizations must pay for access. This creates a notable financial burden for bigger teams.
Docker's pricing has also evolved to reflect broader market trends. Between late 2024 and 2025, Docker bundled its services - Docker Hub, Build Cloud, Scout, and Testcontainers Cloud - into a single subscription package. This came with higher per-user rates: Pro at $9 and Team at $15 per user per month. Additionally, it introduced consumption-based pricing for Docker Hub image pulls and storage, impacting the top 3% of commercial accounts. The Business tier, priced at $24 per user per month, stayed the same but added features like centralized management, RBAC, SAML SSO, and SOC 2 compliance.
Despite these costs, Docker remains dominant, with 67% of developers still using it, compared to just 19% for Podman. Its extensions marketplace, featuring over 100 add-ons like Lens and Snyk, along with VirtioFS file syncing for macOS and smooth WSL integration, helps Docker Desktop stay competitive. For smaller teams, the tool remains an obvious choice. But for larger enterprises, the steep licensing fees make Podman's free alternative an increasingly attractive option.
Podman: Rootless, Daemonless, and Docker-Compatible
As container needs evolve and Docker faces licensing hurdles, Podman has stepped up as a secure and efficient alternative. Unlike Docker, Podman uses a fork–exec model, running each container as an independent user process, without relying on a central daemon. This setup means that when idle, Podman uses almost no additional RAM .
One of Podman’s standout features is its rootless-by-default design, which significantly enhances security. By leveraging Linux user namespaces, Podman maps the container’s root (UID 0) to an unprivileged user on the host system. This ensures that even if a container is compromised, attackers only gain the limited privileges of that unprivileged user . While Docker does offer a rootless mode, it requires additional configuration, whereas Podman makes it the default .
For teams familiar with Docker, Podman offers 95%–99% CLI compatibility. Commands like podman run -d nginx, podman build -t app ., and podman ps function just as they do in Docker. This means developers can alias docker=podman and run existing scripts without any changes. Both tools adhere to OCI standards, ensuring seamless image sharing and compatibility . This makes switching to Podman straightforward and opens the door to integrating it with modern IDEs and tools.
Podman also provides a Docker-compatible API socket (podman.socket), enabling third-party tools and IDEs to connect without issue . For example, Visual Studio 2026 now supports Podman natively, automatically detecting it for containerized application debugging. Additionally, Podman Desktop, a free and open-source alternative to Docker Desktop, has gained significant traction, surpassing 3 million downloads by February 2026.
Switching from Docker to Podman is relatively quick, with most teams completing the transition in just one to two weeks. This shift is often driven by Podman’s performance and security benefits. For instance, Podman’s container startup time averages 0.8 seconds, compared to Docker’s 1.2 seconds - a 33% improvement. By 2025, 34% of organizations reported using multiple container runtimes, often combining Docker for development with Podman for CI/CD workflows. This dual-runtime approach highlights Podman’s growing role in modern container ecosystems.
Architecture Differences: Daemon vs Daemonless, Root vs Rootless
Understanding how Docker and Podman are built sheds light on their strengths and weaknesses in terms of performance and security as of 2026.
Daemon vs Daemonless
Docker operates with a client-server model. The CLI communicates with a persistent daemon (dockerd), which handles containers, images, and networks. Even when idle, the Docker daemon typically consumes between 140–180 MB of RAM.
Podman takes a different approach with its daemonless fork-exec model. Each podman command runs independently, launching containers as child processes of the user. These processes interact with the Linux kernel and image registries via a container monitor called conmon.
This difference in architecture has real-world implications. Docker's centralized daemon creates a single point of failure; if dockerd crashes or restarts, all containers it manages on that node may stop. Podman avoids this issue because its container processes are independent. A failure in one process doesn’t affect others, making Podman a strong choice for high-availability production environments or edge computing setups.
"The Docker socket is one of the most exploited attack vectors in container environments: gaining access to
/var/run/docker.sockgives an attacker full control over the host."
- DevTools Research
This fundamental architectural difference is key to understanding how these tools handle user privileges.
Root vs Rootless
Security in container runtimes is also shaped by how they manage user privileges.
Docker traditionally runs its daemon with root privileges by default, which can introduce risks like privilege escalation through the Docker socket. While Docker does offer a rootless mode, adoption has been low - only 8% of users had enabled it by 2025, likely due to the extra configuration it requires.
Podman, in contrast, is rootless by default. It leverages Linux user namespaces to map a container's root user to an unprivileged user ID (UID) on the host. This means that even if a process escapes the container, it inherits minimal privileges. Podman also assigns fewer kernel capabilities by default - 11 compared to Docker’s 14 - reducing its attack surface.
However, running Podman rootlessly comes with some trade-offs. For example, containers cannot use ports below 1024 unless the system's net.ipv4.ip_unprivileged_port_start setting is modified. That said, with the introduction of the pasta networking backend in Podman 4.0, rootless containers can now achieve about 97% of native network performance.
Comparison Table
Feature
Docker Engine 29
Podman 5.8
Architecture
Client-Server (Daemon-based)
Fork-Exec (Daemonless)
Root Requirement
Yes (runs as root by default)
No (rootless by default)
Idle RAM Usage
140–180 MB
0 MB
Startup Latency
~1.2 seconds
~0.8 seconds
Failure Risk
Single point of failure
Independent processes
Scaling (100+ containers)
Slight performance degradation
Linear performance
Systemd Integration
Limited (requires custom files)
Native (via Quadlets)
Default Capabilities
14
11
These differences in architecture and privilege handling set the stage for deeper discussions on topics like compose functionality, Kubernetes integration, and security in CI/CD workflows.
Docker Compose vs Podman Compose: Feature Parity in 2026
For teams managing multi-container applications, Docker Compose has long been the go-to tool for orchestration. But with Podman emerging as a popular alternative, many are asking: Can Podman handle the same workflows without requiring major changes to your YAML configurations?
As of 2026, Podman offers three ways to work with Compose files: the podman-compose Python wrapper (covering about 85% of the Docker Compose spec), the built-in podman compose command (around 90% coverage), and using the Docker Compose binary with Podman’s UNIX socket. The last option provides the closest compatibility with Docker Compose workflows.
That said, there are still some differences to consider. For example, podman-compose doesn’t support depends_on: condition: service_healthy, a feature available in Docker Compose v2 and v5. Networking is another area where the tools diverge. Docker uses bridge networks, giving each service its own IP and DNS name. In contrast, Podman pods share a network namespace, meaning containers communicate via localhost instead of service names and cannot bind to the same port simultaneously.
Feature
Docker Compose (v5)
Podman Compose (Built-in)
podman-compose (Python)
Spec Coverage
100% (Native)
~90%
~85%
Health Check Conditions
Fully Supported
Limited
Often Unsupported
Service Scaling
Native (--scale)
Not supported in pods
Not supported in pods
Networking Model
Bridge (Isolated IPs)
Shared Namespace (Pods)
Basic Bridge
Kubernetes Export
Via 3rd party (kompose)
Native (generate kube)
Not Native
Root Requirement
Typically Root
Rootless by Default
Rootless by Default
These distinctions are important when deciding whether to transition from Docker Compose to Podman. For instance, if you rely on advanced features like health checks or service scaling, you might find Podman’s current limitations challenging. However, Podman’s secure, rootless design and built-in Kubernetes export (podman generate kube) make it appealing for teams prioritizing modern workflows and security compliance.
If seamless migration is your goal, the best approach is to configure Podman’s UNIX socket and set the DOCKER_HOST environment variable to point to it. This allows you to continue using the Docker Compose CLI while leveraging Podman’s backend. This setup is especially useful for teams with complex YAML configurations or features like profiles that would otherwise require significant rework.
For additional functionality, consider tools like Quadlets for systemd integration or Podman’s Kubernetes export capabilities. These options make Podman a strong choice for Kubernetes-focused projects or environments requiring rootless execution.
Kubernetes Integration: Docker vs Podman vs containerd vs CRI-O

Containerd dominates Kubernetes clusters, powering about 95% of them. It’s the default runtime for major services like AWS EKS, Google GKE, and Azure AKS. Plus, it boasts a startup speed that's up to 20% faster than the now-retired dockershim.
Docker’s role in Kubernetes diminished after the removal of dockershim in Kubernetes v1.24. Now, Docker containers rely on containerd as their backend to function within Kubernetes.
CRI-O, on the other hand, is a Kubernetes-native runtime designed specifically for the Container Runtime Interface (CRI). It’s especially prominent in Red Hat OpenShift environments, where its tight integration with Kubernetes workflows makes it a strong alternative to containerd.
Podman stands out in Kubernetes-native development workflows. Unlike production-focused runtimes, Podman shines in local development settings. Its built-in pod concept and commands like podman generate kube and podman play kube allow developers to create and test Kubernetes YAML manifests without needing a full cluster setup. This eliminates the need for additional tools like kompose. As Destiny Erhabor from freeCodeCamp puts it:
"If you learn Podman pods, you're learning Kubernetes networking too".
Here’s a quick comparison of these runtimes and their roles in Kubernetes:
Runtime
Kubernetes Role
Memory Usage
Primary Use Case
Kubernetes YAML Support
containerd
Default Production Runtime
~30MB
Production clusters, cloud platforms
Via Kubernetes orchestrator
CRI-O
K8s-Native Production Runtime
Minimal
OpenShift, production Kubernetes
Via Kubernetes orchestrator
Podman
Dev Tool (K8s-Native)
0MB (daemonless)
Local Kubernetes development, CI/CD
Native (generate/play kube)
Docker
Deprecated (via containerd)
~100MB
Legacy development environments
Via third-party tools
Interestingly, many teams adopt a hybrid approach. Around 34% of organizations use Docker for development, Podman for CI pipelines, and containerd for production Kubernetes. This balance reflects a broader trend: prioritizing development flexibility while optimizing performance for production.
Security Comparison: Rootless Containers, SELinux, and Seccomp Profiles
When it comes to security, the differences between Docker and Podman become even more pronounced. Podman takes a fundamentally different approach compared to Docker, especially with its default rootless mode. By 2025, only 8% of Docker users were running containers in rootless mode, whereas Podman ships with rootless mode enabled by default. This design choice significantly reduces the risk in case of a container escape. If a Podman container is compromised, the attacker is limited to unprivileged access. By contrast, a typical Docker container escape can lead to root access due to Docker's root-privileged daemon.
One of Docker's major vulnerabilities lies in its reliance on a privileged socket. The Docker socket (/var/run/docker.sock) is a critical weakness because gaining access to it essentially provides root control over the host system. As security expert Mehdi BAFDIL puts it:
"The Docker daemon running on your production servers right now? It's a root-privileged security time bomb waiting to go off."
SELinux integration further underscores the security gap. Podman automatically applies Multi-Category Security (MCS) labels to each container, which prevents lateral movement even when containers share resources. While Docker also supports SELinux, it often requires manual configuration to achieve similar results. For example, Podman users on RHEL or Fedora can easily enforce proper security contexts by appending :Z for private labels or :z for shared labels to volume configurations. This automatic SELinux enforcement, combined with Podman’s reduced kernel capabilities, creates a more secure environment.
Speaking of kernel capabilities, Podman defaults to 11, compared to Docker's 14. Docker’s additional capabilities, such as CAP_NET_RAW and CAP_AUDIT_WRITE, increase the potential attack surface. With 38% of CVEs in 2025 classified as High or Critical severity, these differences in default settings carry real-world consequences for production systems.
Seccomp profiles also play a key role in container security by limiting the system calls a container can execute, which helps mitigate kernel-level exploits. Both Docker and Podman include default seccomp policies, but Docker’s often require manual adjustments, whereas Podman’s integration is smoother and more automatic. These security measures collectively position Podman as a safer choice for containerized environments.
Security Feature
Docker Engine 29
Podman 5.8
Default User Mode
Rootful (Rootless requires setup)
Rootless by default
Architecture
Centralized Root Daemon
Daemonless (Fork-exec)
Kernel Capabilities
14 (Default)
11 (Default)
SELinux/AppArmor
Supported (Manual config)
Native (Out-of-the-box)
Primary Attack Vector
Docker Socket (/var/run/docker.sock)
User-level process vulnerabilities
Container Escape Impact
Potential host root access
Limited to unprivileged user permissions
Developer Experience: CLI Compatibility, IDE Integration, and Debugging
Podman’s command-line interface (CLI) closely mirrors Docker’s, making it easy for developers to transition. You can even alias docker to podman and continue using familiar commands like run, build, ps, exec, and logs. On top of that, Podman introduces Kubernetes-focused commands such as podman pod and podman generate kube, which aren’t natively available in Docker. This compatibility ensures a smooth user experience while offering extra functionality tailored for Kubernetes workflows.
When it comes to performance, Podman has its advantages. Containers start about 33% faster with Podman (0.8 seconds versus Docker’s 1.2 seconds), and it uses zero idle RAM, compared to Docker’s 140–180 MB. However, Docker’s BuildKit still edges out Podman for complex builds, completing them 5–10% faster. These differences largely stem from Podman’s daemonless architecture, which avoids the overhead of initializing a background service.
Podman’s growing integration with development environments further enhances its appeal. Visual Studio 2026, for instance, now supports Podman natively, automatically detecting the active runtime to help developers create, run, and debug containerized applications. Other popular IDEs like VS Code and JetBrains also work seamlessly with Podman. Developers just need to enable the Podman socket and set DOCKER_HOST. While Docker Desktop continues to shine with its sleek GUI, integrated debugging tools, and Extensions Marketplace, Podman Desktop - surpassing 3 million downloads by February 2026 - provides a free, feature-packed alternative that’s steadily closing the gap.
Debugging workflows remain consistent across both platforms. Developers can attach remote debuggers for languages like Python (via debugpy), Node.js (using the --inspect flag), Java (with JDWP), and Go (using Delve) by exposing the necessary ports and connecting their IDEs. Podman also offers additional tools for low-level debugging, such as strace and nsenter for namespace access, along with native integration with journald for advanced log analysis using journalctl.
Despite these advancements, Docker still dominates, with 67% of developers using it as their primary tool. Podman’s CLI speed and thoughtful IDE integration make it a strong contender, especially in environments prioritizing security and cost-efficiency. However, Docker retains its position as the go-to option for many, thanks to its robust ecosystem and widespread compatibility. As DevTools Research aptly puts it:
"Docker remains the gold standard for developers: the best DX, the largest ecosystem, and the widest support across tools and cloud platforms".
For developers comfortable with a more hands-on approach, Podman offers solid productivity gains and avoids licensing costs, making it an increasingly viable alternative.
CI/CD Pipelines: Docker vs Podman in GitHub Actions and GitLab CI
CI/CD pipelines thrive on three key factors: security, resource efficiency, and build speed. Docker often relies on Docker-in-Docker (DinD) with privileged mode for containerized runners, introducing potential security risks through the /var/run/docker.sock socket . Podman, however, operates without a daemon, allowing rootless builds and better isolation on shared runners .
For GitHub Actions, Podman is pre-installed on the ubuntu-latest runners, making it an easy substitute for Docker commands. On the other hand, GitLab CI workflows using Docker often require the docker:dind service along with TLS configuration. In contrast, Podman workflows can use a stable image, such as quay.io/podman/stable, with minimal setup, reducing complexity and speeding up pipeline configuration .
Performance benchmarks highlight Podman’s strengths in container startup speed and memory efficiency. Podman uses zero idle RAM, while Docker has a higher memory footprint . For workloads with over 100 concurrent containers, Podman maintains consistent performance, while Docker shows slight performance drops. However, Docker’s BuildKit outpaces Podman by 5–10% in complex multi-stage builds and pulls large images about 10% faster due to its optimized caching .
Here’s how they compare on key metrics:
Metric
Docker 29.3.1
Podman 5.8.1
Winner
Cold Startup Time
~1.2s
~0.8s
Podman
Idle Memory (Engine)
140–180 MB
0 MB
Podman
Image Pull (1 GB)
~12s
~13s
Docker
Build Speed (Cached)
Baseline
5–10% slower
Docker
Scaling (100+ Containers)
Slight degradation
Linear performance
Podman
For production CI/CD environments prioritizing security and resource efficiency, Podman offers clear advantages. As Nawaz Dhandala explains:
"Updating CI/CD pipelines from Docker to Podman eliminates the need for a container daemon, improves security with rootless builds, and simplifies pipeline runner configuration".
That said, Docker’s BuildKit remains a strong contender for multi-stage builds requiring speed. To avoid disk space issues on shared runners, adding podman system prune -f as a post-build cleanup step is recommended. These factors are essential when determining the best container runtime for your CI/CD pipelines.
Decision Matrix: When to Use Docker vs Podman
Building on the earlier comparison of architecture and security, this decision matrix simplifies the choice between Docker and Podman. In 2026, your decision should hinge on factors like team size, security priorities, and licensing costs. For small teams (under 250 employees and less than $10 million in annual revenue), Docker Desktop offers an excellent developer experience within its free tier. Larger enterprises, however, will need to account for licensing fees ranging from $9 to $24 per user per month. Podman, on the other hand, remains free under the Apache 2.0 license.
For industries with strict security requirements - such as finance or healthcare - Podman’s rootless architecture stands out. By eliminating the privileged Docker socket, it removes a common attack vector in containerized environments. Developers working with Kubernetes will also appreciate Podman’s native pod support and its generate kube command, which simplifies moving from local development to Kubernetes cluster deployment.
However, Docker is still the go-to option for teams relying on Docker Swarm, as Podman lacks support for Swarm orchestration. Additionally, for legacy setups involving Docker Compose, Docker’s ecosystem and BuildKit’s faster build speeds (5–10% quicker) make it a practical choice.
Many organizations are adopting a hybrid approach: Docker for local development, and Podman for production and CI/CD pipelines. This strategy combines Docker Desktop’s user-friendly interface with Podman’s lightweight, daemon-less architecture and strong security features.
Here’s a quick decision matrix to help teams choose between Docker and Podman:
Use Case
Recommended Tool
Primary Reason
Solo Dev / Small Team
Docker
Polished GUI and developer-friendly experience (Docker Desktop).
Large Enterprise
Podman
Avoids per-user licensing fees.
Regulated Industries
Podman
Rootless architecture meets strict security standards.
Kubernetes-Native Dev
Podman
Built-in pod support and Kubernetes YAML generation.
CI/CD Pipelines
Podman
Better isolation on shared runners without privileged mode.
Legacy Docker Swarm
Docker
Podman doesn’t support Swarm orchestration.
High-Density Scaling
Podman
Lower per-container overhead ensures efficient scaling.
Migrating from Docker to Podman can present challenges, such as handling legacy scripts that access /var/run/docker.sock, volume permission issues, or complex Docker Compose files. Fortunately, using alias docker=podman addresses most CLI compatibility concerns, and podman unshare chown resolves UID mapping problems. For most teams, the migration process typically takes 1–2 weeks.
Conclusion
Choosing between Docker and Podman in 2026 ultimately comes down to balancing your technical requirements with your business priorities. Docker continues to dominate as the go-to option for local development, offering a robust presence in production and CI/CD pipelines. Its rootless, daemonless architecture provides strong security features and efficient resource management.
Key factors like developer experience, security, and cost play a pivotal role in making this decision. For smaller teams (under 250 employees), Docker Desktop's free tier provides access to its top-tier tools without additional expense. However, for larger enterprises, licensing costs can climb to approximately $50,400 per year for 200 engineers. In such cases, Podman emerges as an appealing free alternative.
Organizations in highly regulated industries - such as fintech, healthcare, and government - may lean toward Podman for its rootless design, which eliminates the need for a privileged daemon socket. On the other hand, teams already entrenched in Docker Swarm or managing complex legacy Compose workflows may find Docker to be the more practical choice.
Interestingly, a hybrid approach has gained traction, with 34% of organizations opting to use Docker for local development while deploying Podman in production. This method combines the strengths of both tools, improving developer experience while benefiting from Podman’s zero idle resource consumption.
There’s no universal answer to this decision. Your choice should reflect your team’s workflows, security considerations, and budget constraints. Both Docker and Podman are mature, production-ready solutions in 2026. To simplify your evaluation, refer to the decision matrix provided earlier for a side-by-side comparison of their use cases.
FAQs
Can I use Podman without changing my Docker scripts?
Podman supports Docker-compatible CLI commands, meaning you can usually run most Docker scripts without altering them. However, because Podman uses a daemonless and rootless architecture, you might need to tweak scripts that depend on Docker-specific features. For standard Docker commands, though, Podman often works as an easy substitute with only minor adjustments required.
What breaks when switching from Docker Compose to Podman Compose?
Switching to Podman Compose might create some hiccups when it comes to compatibility with certain commands and features. While Docker Compose provides more extensive functionality and seamless integration with Docker, Podman Compose does its best to support most Docker Compose commands. However, some of the more advanced or less frequently used features may not function as intended.
If you're dealing with complex setups or relying on specific options, you might encounter some differences or limitations. It's worth keeping this in mind when considering a switch, as these discrepancies could impact your workflow.
How do I migrate CI pipelines from Docker-in-Docker to rootless Podman?
Switching from Docker-in-Docker (DinD) to rootless Podman involves a few key steps:
- Replace all
dockercommands in your pipeline scripts withpodman. - Update build processes to use
podman buildinstead ofdocker build. - Configure rootless mode by setting up user namespaces. This ensures Podman operates without requiring root privileges.
Thorough testing in a staging environment is crucial. Pay close attention to areas like volume mounting, networking, and systemd compatibility, as these can behave differently in Podman compared to Docker.
If your pipeline relies on tools like Docker Compose, you may need to adjust. For example, consider using podman-compose or other compatible alternatives to handle multi-container setups.
Related Blog Posts
- Top 9 Container Registries 2024: How to Choose
- Docker Container Lifecycle Management: Best Practices
- Kubernetes CNI Comparison: Flannel vs Calico vs Canal
- DevOps Feedback Loops: Quality Guide 2024
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":\[{"@type":"Question","name":"Can I use Podman without changing my Docker scripts?","acceptedAnswer":{"@type":"Answer","text":"
Podman supports Docker-compatible CLI commands, meaning you can usually run most Docker scripts without altering them. However, because Podman uses a daemonless and rootless architecture, you might need to tweak scripts that depend on Docker-specific features. For standard Docker commands, though, Podman often works as an easy substitute with only minor adjustments required.
"}},{"@type":"Question","name":"What breaks when switching from Docker Compose to Podman Compose?","acceptedAnswer":{"@type":"Answer","text":"Switching to Podman Compose might create some hiccups when it comes to compatibility with certain commands and features. While Docker Compose provides more extensive functionality and seamless integration with Docker, Podman Compose does its best to support most Docker Compose commands. However, some of the more advanced or less frequently used features may not function as intended.
If you're dealing with complex setups or relying on specific options, you might encounter some differences or limitations. It's worth keeping this in mind when considering a switch, as these discrepancies could impact your workflow.
"}},{"@type":"Question","name":"How do I migrate CI pipelines from Docker-in-Docker to rootless Podman?","acceptedAnswer":{"@type":"Answer","text":"Switching from Docker-in-Docker (DinD) to rootless Podman involves a few key steps:
- Replace all
dockercommands in your pipeline scripts withpodman. - Update build processes to use
podman buildinstead ofdocker build. - Configure rootless mode by setting up user namespaces. This ensures Podman operates without requiring root privileges.
Thorough testing in a staging environment is crucial. Pay close attention to areas like volume mounting, networking, and systemd compatibility, as these can behave differently in Podman compared to Docker.
If your pipeline relies on tools like Docker Compose, you may need to adjust. For example, consider using podman-compose or other compatible alternatives to handle multi-container setups.
"}}]}


