
Define clear security roles, source candidates from CTFs/bug bounties and conferences, and use hands-on tests plus competitive pay.
The cybersecurity hiring challenge is real: 4.8 million positions remain unfilled globally, and roles take 21% longer to fill compared to other tech jobs. Why? Misaligned hiring practices, skill gaps, and the complexity of finding qualified candidates in this fast-evolving field. Here's what you need to know:
- Define roles clearly: "Cybersecurity Engineer" can mean five different specialties (e.g., Security Engineer, Penetration Tester, SOC Analyst). Mislabeling wastes time and resources.
- Avoid traditional job boards: Platforms like LinkedIn often fail due to clearance requirements, privacy concerns, and keyword mismatches.
- Go where talent is: Look at CTF platforms (HackTheBox, TryHackMe), bug bounty sites (HackerOne, Bugcrowd), or security events (DEF CON, BSides).
- Test practical skills: Focus on hands-on assessments like threat modeling, code reviews, and incident response simulations over trivia or certifications alone.
- Offer competitive pay: Salaries range from $75K for entry-level roles to $500K+ for CISOs, with cloud security and AI expertise commanding premiums.
- Retain talent: Provide career growth, training budgets, flexible work options, and access to industry events to keep your team engaged.
Hiring cybersecurity professionals requires precision and proactive strategies. Get specific about your needs, engage with niche communities, and prioritize hands-on expertise to build a strong team.
Cybersecurity Role Types Explained
::: @figure 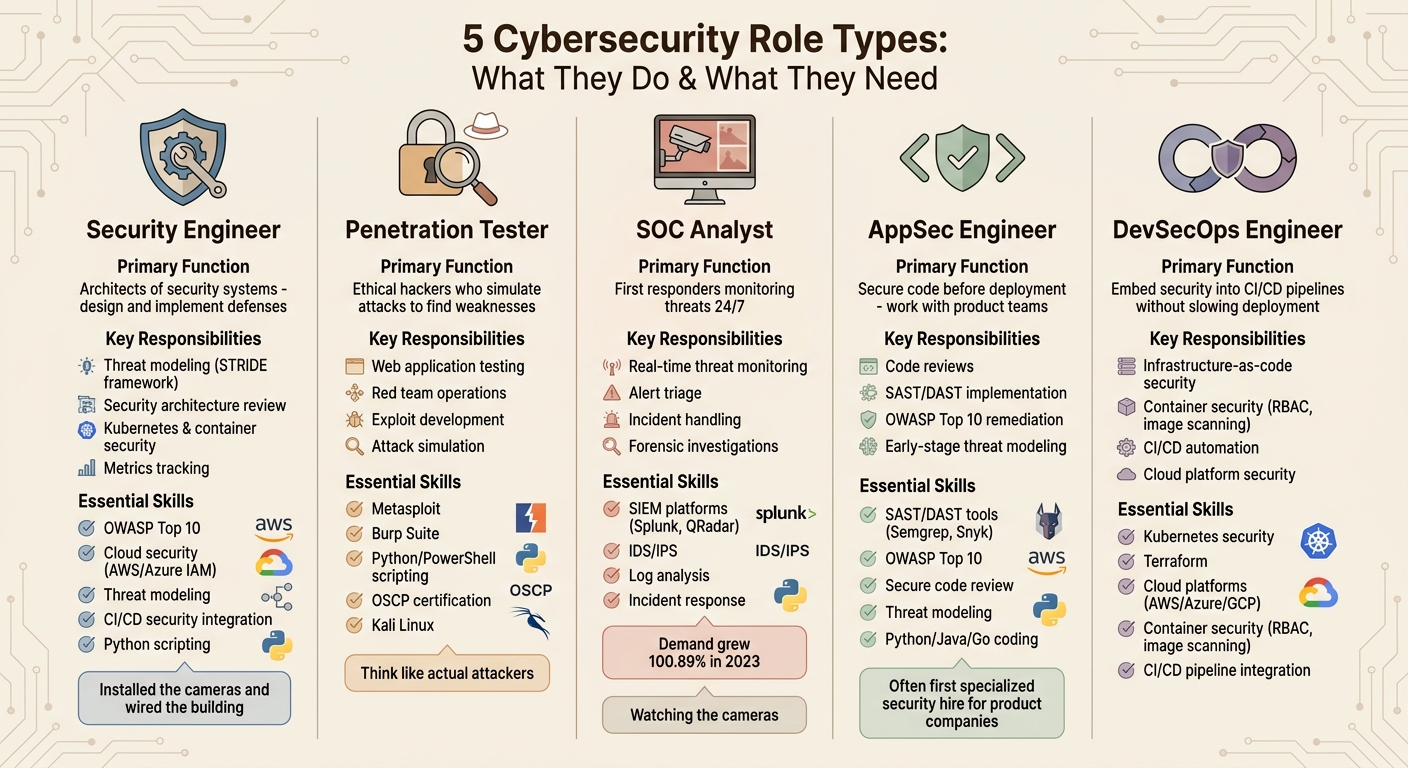 {5 Cybersecurity Role Types: Skills, Responsibilities, and Key Tools Compared}
{5 Cybersecurity Role Types: Skills, Responsibilities, and Key Tools Compared}
Before you post a job listing for a "cybersecurity engineer", it’s important to pin down exactly what the role entails. This title can refer to at least five distinct positions, each with its own skill set, tools, and responsibilities. Misidentifying the role can lead to wasted time, unnecessary costs, and dangerous gaps in your security defenses. Defining these roles clearly will streamline your hiring process and help you avoid costly mistakes. Beyond role definition, adopting modern candidate sourcing tactics is essential for reaching top-tier talent.
Security Engineer
Security Engineers are the architects of your security systems. They design and implement the defenses that protect your organization - everything from firewalls and encryption protocols to endpoint protection and authentication frameworks. Their work is proactive, aiming to spot and address vulnerabilities before they become an issue.
"If the analyst watches the cameras, the engineer installed them and wired the whole building." - KORE1
Their responsibilities include threat modeling with frameworks like STRIDE, reviewing security architectures, managing Kubernetes and container security, and tracking metrics to measure the effectiveness of these defenses. For companies with growing development teams, hiring a specialized Application Security (AppSec) Engineer to focus on product security becomes increasingly important.
Key skills: Familiarity with the OWASP Top 10, cloud security (AWS or Azure IAM), threat modeling, CI/CD security integration, and Python scripting.
Penetration Tester
Penetration Testers, or ethical hackers, simulate attacks to identify weaknesses in your systems. Unlike Security Engineers who build defenses, Penetration Testers actively test those defenses by mimicking attacker behavior.
They specialize in web application testing, red team operations, and exploit development, using tools like Metasploit, Burp Suite, and Kali Linux. These professionals often approach problems with an attacker’s mindset, which can make them stand out - or feel unconventional - in traditional corporate settings.
"The best pen testers think like actual attackers, which honestly makes them a little unusual in traditional interview settings. That weirdness is the point." - KORE1
Most companies hire penetration testers through external firms to ensure an unbiased evaluation of their security measures.
Key skills: Expertise in Metasploit, Burp Suite, Python/PowerShell scripting, and certifications like OSCP.
SOC Analyst
Security Operations Center (SOC) Analysts are your first responders to real-time threats. They monitor critical systems 24/7, triage alerts from tools like Splunk or QRadar, and handle incidents as they arise. Think of them as the ones "watching the cameras" installed by Security Engineers.
Their daily tasks involve logging events, using security tools, and performing forensic investigations after incidents. With the constant influx of alerts, SOC Analysts need sharp analytical skills to separate genuine threats from false positives.
The demand for SOC Analysts grew by 100.89% in 2023, driven by the industry’s increasing focus on reactive security measures. When hiring for this role, look for candidates who can stay calm under pressure - vetting technical skills means little if someone panics during a breach .
Key skills: Experience with SIEM platforms (Splunk, QRadar), IDS/IPS, log analysis, and incident response.
Application Security (AppSec) Engineer
AppSec Engineers work directly with product teams to secure code before it’s deployed. They conduct code reviews, use tools like SAST and DAST (e.g., Semgrep or Snyk), and address vulnerabilities - such as those in the OWASP Top 10 - during the design phase. This "shift-left" approach ensures issues are fixed early, saving time and money.
For companies focused on product development, an AppSec Engineer is often the first specialized security hire . They collaborate closely with developers to promote secure coding practices and perform early-stage threat modeling.
Key skills: Proficiency with SAST/DAST tools, a strong grasp of the OWASP Top 10, secure code review expertise, threat modeling, and coding skills in languages like Python, Java, or Go.
DevSecOps Engineer
DevSecOps Engineers combine security with DevOps, embedding safeguards into CI/CD pipelines to maintain security without slowing down deployments. They focus on securing infrastructure-as-code, implementing container security measures like RBAC and image scanning, and automating tests throughout the CI/CD process.
This role requires a mix of security knowledge and DevOps expertise. DevSecOps Engineers work with tools like Terraform, Kubernetes, and cloud platforms (AWS, Azure, GCP) to ensure security is integrated at every stage of deployment.
Key skills: Experience with Kubernetes security, Terraform, cloud platforms (AWS/Azure/GCP), container security practices (RBAC, image scanning), and CI/CD pipeline integration.
Once you’ve defined the role you need, the next step is understanding why traditional job boards and LinkedIn might not be the best tools for finding these specialized professionals.
sbb-itb-d1e6221
Why Job Boards and LinkedIn Don't Work for Security Hiring
Finding the right candidates for cybersecurity roles can feel like searching for a needle in a haystack. If your first instinct is to post on LinkedIn or a general job board, you might want to think again. These platforms often fall short when it comes to cybersecurity hiring, and it's not just about supply and demand. Three key challenges - clearance requirements, privacy concerns, and vague skill representation - make traditional platforms ineffective for this field.
Clearance Requirements Shrink the Talent Pool
A major hurdle in cybersecurity hiring is the need for security clearances, especially for roles in defense, government contracting, or critical infrastructure. These clearances are rare, and professionals who have them often avoid advertising their status or work history on public platforms like LinkedIn. Why? It’s a security risk. They’re wary of being targeted by foreign intelligence or malicious actors .
Job boards also don’t have a way to verify clearance levels, which leads to mismatches. For example, if a role requires Top Secret/SCI clearance and a candidate doesn’t already have it, the onboarding process can be delayed for months - or even years - due to the extensive SF-86 investigation . Financial issues are the most common reason candidates fail to obtain or keep a clearance , and traditional platforms can’t screen for these factors. This often results in wasted time and effort for both employers and candidates.
On top of that, employers are looking for "unicorn" candidates - those who combine advanced clearances with expertise in cutting-edge fields like AI-driven defense. With over 500,000 unfilled cybersecurity jobs in the U.S. , this bottleneck is a serious issue.
Privacy-Conscious Professionals Avoid Traditional Outreach
Cybersecurity experts are, by nature, privacy-conscious. They know the risks of exposing personal data better than anyone, which makes them skeptical of unsolicited messages. Many top-tier professionals aren’t actively job hunting or maintaining high-visibility profiles - they’re focused on their work .
High-demand specialists, such as cloud security engineers, are often overwhelmed by messages from recruiters, leading to what’s known as "communication fatigue" . These professionals tend to respond only to trusted contacts or well-established networks. They’re more impressed by tangible achievements like GitHub contributions, bug bounty results, or Capture The Flag (CTF) rankings than by generic job descriptions on LinkedIn .
Because of this, many cybersecurity professionals gravitate toward niche communities like subreddits (e.g., r/netsec), Discord servers, or Slack groups. These spaces allow them to engage in technical discussions without the noise of traditional recruiting tactics . In fact, 91% of recruiters using specialized AI tools have reduced or stopped using LinkedIn Recruiter because keyword-based searches fail to capture the complexity of security skills . This shift highlights the need for alternative, more tailored sourcing methods.
Specialized Skills Are Hard to Spot in Standard Searches
Even when cybersecurity professionals are on LinkedIn, their profiles often don’t tell the full story. The way they describe their skills can vary widely depending on the tools they use or the threats they’ve faced. This creates "visibility problems", where qualified candidates are overlooked because their profiles don’t match rigid keyword searches .
Adding to the challenge, job boards often filter candidates based on certifications like CISSP or CISA, even for entry-level roles. This practice can exclude capable candidates who don’t list these credentials, especially since certifications like CISA require five years of experience - far more than what’s typically expected for an entry-level position .
What really matters in cybersecurity are hands-on achievements, like HackTheBox rankings, CVE discoveries, or contributions to open-source projects on GitHub. These metrics provide objective proof of a candidate’s skills, but they’re often missed by traditional keyword filters. This is why specialized platforms that highlight real-world performance are becoming essential for identifying top talent.
With cybersecurity roles taking 21% longer to fill than other IT positions , it’s clear that conventional recruiting methods aren’t just inefficient - they’re actively slowing down the hiring process. To succeed, employers need to connect with candidates in the spaces where they already are: specialized communities and platforms designed for security professionals.
Where to Find Cybersecurity Engineers
Finding skilled cybersecurity professionals often means looking beyond traditional hiring platforms. These experts tend to gather in specialized communities where they can showcase their skills and connect with others who share their passion for security.
CTF Communities and Practice Platforms
Platforms like HackTheBox and TryHackMe are hotspots for cybersecurity talent. These sites not only allow users to hone their skills but also provide leaderboards and rankings that objectively identify qualified technical candidates .
When evaluating candidates, check their profiles on these platforms. Look for consistent activity, high rankings, and detailed write-ups of their problem-solving methods. These indicators provide a much clearer picture of their real-world expertise than a simple resume claim like "proficient in penetration testing" .
Bug Bounty Platforms
For proven security researchers, HackerOne and Bugcrowd are great resources. These platforms maintain public "hall of fame" lists that highlight individuals who have consistently identified and disclosed critical vulnerabilities. Success on these platforms is a strong indicator of a candidate's ability to deliver impactful results .
"HackTheBox rankings and HackerOne/Bugcrowd hall-of-fame entries provide objective, public validation of security capability. These signals are far more reliable than self-reported resume claims." - StepTo
Bug bounty profiles also reveal areas of expertise, such as web application security, mobile app vulnerabilities, or cloud infrastructure. This makes it easier to align candidates with your specific needs. Additionally, these professionals are accustomed to working independently, documenting their findings, and communicating effectively with both technical teams and non-technical stakeholders.
Security Conferences
Events like DEF CON, Black Hat, and BSides are where the cybersecurity community gathers in person. These conferences feature research presentations, on-site CTF competitions, and discussions about the latest threats and defenses. Attending these events gives you direct access to potential candidates who might not respond to traditional outreach .
When recruiting at conferences, authenticity is key. Security professionals can easily spot recruiters who lack genuine interest. Instead of handing out generic job descriptions, engage in meaningful conversations about tools, methodologies, and current challenges. Ask about their research, favorite CTF experiences, or thoughts on emerging threats. Building relationships first often leads to successful recruiting later .
BSides events, in particular, offer a more intimate setting and tend to focus on local communities. They're also more budget-friendly to sponsor, making them a smart choice for startups or mid-sized companies looking to establish their presence in the security field .
Security-Focused Slack and Discord Groups
Many cybersecurity professionals participate in niche Slack workspaces and Discord servers dedicated to areas like incident response, cloud security, and penetration testing. These communities foster real-time collaboration, knowledge sharing, and problem-solving .
Reddit is another valuable resource. Subreddits like r/netsec and r/cybersecurity host technical discussions, research sharing, and career advice. Observing how candidates interact in these forums can provide insight into their problem-solving skills, willingness to help others, and ability to stay updated on emerging threats - qualities that a resume alone can't reveal .
However, gaining access to these spaces can be tricky. Many are invite-only or require active participation before you can start recruiting. Building trust and contributing meaningfully to these communities is essential if you want to connect with their members .
daily.dev Recruiter
daily.dev Recruiter offers a fresh approach to finding cybersecurity professionals. Instead of relying on outdated profiles or cold outreach, this platform connects you with candidates based on their actual reading habits and community activity. With over 1 million developers - including security engineers - using daily.dev to stay informed on topics like AppSec, DevSecOps, and threat intelligence, it's a goldmine for finding engaged professionals.
The platform ensures every introduction is double opt-in, meaning candidates have already expressed interest in opportunities like yours. This reduces privacy concerns and communication fatigue while connecting you with candidates who are actively learning and signaling their interests through the content they consume.
You can even filter candidates by specific security domains, such as cloud security, penetration testing, or zero-day vulnerabilities. By leveraging daily.dev’s active developer network, you can find professionals in real time, offering a more dynamic and effective alternative to traditional recruiting methods.
How to Test Cybersecurity Candidates
Closing the cybersecurity talent gap means focusing on testing candidates' practical skills. In fact, 84% of cybersecurity hiring managers now rely on skills-based assessments during the hiring process . After all, a resume alone can’t prove someone is ready to detect SQL injections or handle active incidents.
The primary objective? Assess problem-solving skills, not rote memorization. For example, provide vulnerable code - like Python Flask or Node.js - with flaws such as SQL injection, IDOR, or SSRF. Have candidates identify and explain these vulnerabilities. This reveals their thought process and how effectively they can communicate security risks .
Threat modeling sessions are another effective method. Present a system diagram, such as an e-commerce checkout flow or a CI/CD pipeline, and ask candidates to identify potential threats using frameworks like STRIDE or PASTA. This approach evaluates their ability to think like an attacker and prioritize risks .
For incident response roles, create scenarios based on real-world breaches. For instance, describe unusual outbound traffic, ransomware indicators, or compromised credentials. Then, ask candidates to outline their first five actions. This tests their ability to stay composed, make decisions under pressure, and manage containment, investigation, and communication . These practical exercises align closely with the daily responsibilities of cybersecurity professionals.
Skills to Test
Hands-on exercises are key to evaluating a candidate's readiness. For application security (AppSec) roles, ask candidates to intercept and modify requests in Burp Suite during a live demonstration. For cloud security positions, have them analyze an AWS IAM policy for over-permissioned roles or identify misconfigured S3 buckets .
Provide real application code and ask them to uncover vulnerabilities tied to the OWASP Top 10. Pay close attention to how they explain their findings - security engineers must effectively communicate risks to developers and business leaders alike .
Tool-based assessments are another excellent option. For example:
- Analyze a packet capture for malicious traffic.
- Harden a Linux server.
- Configure Kubernetes RBAC policies.
These tasks show whether candidates can apply industry-standard tools in realistic scenarios .
| Skill Category | Practical Evaluation Method |
|---|---|
| AppSec | Code review for OWASP Top 10; Burp Suite request modification |
| Cloud Security | AWS/Azure IAM policy review; Kubernetes RBAC configuration |
| Threat Modeling | STRIDE/PASTA analysis of a microservices API |
| Incident Response | Live simulation of ransomware containment and communication |
| Automation | Python/Bash scripting for security task automation |
Additionally, assess candidates' ability to explain complex vulnerabilities to non-technical stakeholders. Even the most technical findings are useless if they don’t lead to remediation or organizational action .
What Not to Test
Avoid trivia questions. Multiple-choice tests that ask questions like "What port does HTTPS use?" don’t provide insight into a candidate's ability to exploit vulnerabilities or design secure systems, so consider assessing technical skills without coding tests .
Also, don’t impose unrealistic time constraints. For example, assigning a four-hour task that would realistically take a full day only tests how well someone can rush, not their attention to detail .
Don’t rely solely on certifications. While certifications like CISSP indicate knowledge of security concepts, they don’t necessarily reflect practical skills. A CISSP-certified individual who struggles to read a network capture or write a Burp Suite extension may not be as effective as someone with hands-on experience .
"A CISSP or Security+ certifies knowledge of security concepts - not the ability to find a SQL injection, bypass an authentication check, or configure a Kubernetes admission controller." - StepTo
Practical experience matters most. In fact, 73% of hiring managers prioritize hands-on cybersecurity experience when evaluating candidates .
How to Use Certifications
Certifications still have value, but they should complement, not replace, hands-on skill assessments. Think of them as indicators of knowledge - not definitive proof of ability. For instance, certifications like OSCP (Offensive Security Certified Professional) stand out because they require candidates to complete a 24-hour practical exploitation exam. Similarly, CKS (Certified Kubernetes Security Specialist) demonstrates proficiency in cloud security .
For leadership roles, certifications like CISSP or CISM can highlight broad security knowledge and professional maturity, even if they don’t focus on day-to-day technical tasks .
Interestingly, 89% of hiring managers are open to candidates with only entry-level certifications if they can demonstrate the required skills . This suggests that requiring advanced certifications - like CISSP - for entry-level positions may exclude capable candidates. Certifications like CISA or CISSP often require five years of experience, creating a "qualification catch-22" that locks out new talent .
Instead, focus on practical evaluations like code reviews, threat modeling exercises, and tool-based assessments. This approach ensures you’re building a strong security team by balancing hands-on expertise with formal credentials.
Cybersecurity Salary Ranges and Compensation
Cybersecurity jobs are commanding higher salaries than software engineering roles, with the pay gap continuing to grow. Salaries in this field are increasing by 7% to 10% annually, driven by a global shortfall of 4.8 million unfilled positions in 2024 . With 88% of organizations linking security incidents to skill shortages, companies are fiercely competing to attract talent .
Understanding salary benchmarks is essential for making competitive offers. Robert Ardell from KORE1 highlights this point:
"Six months of an unfilled security engineering seat costs more than the $20K raise that would have closed the candidate" .
While it typically takes 3 to 6 months to fill a cybersecurity position, leading companies reduce this timeline to just 3 to 4 weeks by pre-approving salary ranges before starting their search .
Salary by Experience Level
Salaries in cybersecurity vary based on experience and specialization. For mid-level professionals with 3 to 5 years of experience, pay typically ranges from $110,000 to $175,000 . Senior-level roles can offer base salaries between $145,000 and $270,000, while executives like CISOs often earn over $500,000 when bonuses and equity are included .
Specialized skills significantly influence pay. For example:
- Cloud security engineers earn $15,000 to $30,000 more than network security engineers at the same experience level .
- Professionals with AI/ML security expertise see a 30% to 40% salary boost as companies work to secure large language model deployments .
- Senior penetration testers with offensive security certifications, such as OSCP, and bug bounty experience can earn between $130,000 and $220,000 .
| Role | Experience Level | 2026 Salary Range (US Base) | Key Premium Skills |
|---|---|---|---|
| Security Engineer | Junior (0–2 yrs) | $75,000 – $110,000 | Python, Security+, Cloud Internships |
| Mid-Level (3–5 yrs) | $110,000 – $150,000 | Cloud Security, Automation | |
| Senior (5–8 yrs) | $145,000 – $195,000 | Architecture, Incident Response | |
| Penetration Tester | Junior/Associate | $70,000 – $95,000 | OSCP, Bug Bounty history |
| Mid-Level | $95,000 – $130,000 | Web App Pentesting, OSCP | |
| Senior/Lead | $130,000 – $220,000 | Exploit Dev, Red Teaming | |
| DevSecOps / AppSec | Mid-Level | $120,000 – $160,000 | CI/CD Security, SAST/DAST |
| Senior | $155,000 – $200,000 | Kubernetes, Container Security | |
| Cloud Security Eng. | Mid-Level | $120,000 – $160,000 | AWS/Azure/GCP Security |
| Senior/Architect | $155,000 – $270,000 | Multi-cloud, Zero-Trust | |
| Security Architect | Senior (7+ yrs) | $152,000 – $240,000+ | Zero-Trust, NIST Frameworks |
| CISO | Executive | $220,000 – $500,000+ | Board Reporting, Risk Finance |
What Affects Pay
Several factors shape cybersecurity salaries:
- Location: Cities like San Francisco, New York, and Washington D.C. offer premiums ranging from 10% to 35% above the national average . For instance, San Jose leads with an average security salary of $175,500, followed by Washington state at $150,600 .
- Certifications: Credentials like CISSP can add $25,000 to $35,000 to salaries, with CISSP holders earning a median of $164,000 . Offensive security certifications, such as OSCP, are highly valued for penetration testing roles .
- Security Clearances: Active clearances, especially in regions like Washington D.C., can boost pay by $10,000 to $40,000 .
- Industry: Salaries also vary by sector, with pharmaceutical and biotech companies offering the highest median compensation for security engineers at $205,000, followed by technology at $162,000 and financial services at $154,000 .
As Robert Ardell from KORE1 explains:
"The person who can show the work beats the person who can show the acronym" .
Equity, Bonuses, and Benefits
Competitive compensation in cybersecurity goes beyond base salary. Total pay, including equity and bonuses, can be 20%–40% higher than base salary . In tech leadership roles, equity often makes up about half of the total package . Performance bonuses tied to security metrics, such as reducing response times or passing audits, are becoming more common.
When salary budgets are tight, signing bonuses or equity grants (typically $5,000–$10,000) can make a difference . Covering professional development costs, such as SANS courses (priced between $7,000 and $9,000), shows a commitment to employee growth . In fact, 53% of U.S. employers are willing to increase starting pay for candidates with in-demand skills .
Other benefits, like flexible work arrangements, are now standard. These technical hiring best practices are essential for remaining competitive. Requiring full-time on-site work can immediately shrink the candidate pool . Transparent on-call policies, conference budgets, dedicated research time, and clear career paths - whether for technical or management tracks - are just as vital as cash compensation for retaining top talent.
How to Retain Cybersecurity Talent
Bringing security engineers on board is no small feat - it’s both costly and time-consuming. But losing them? That’s even more expensive. Nearly half (47%) of cybersecurity professionals point to a lack of promotion and development opportunities as a key reason for leaving their roles . To keep your team intact, focus on creating opportunities for growth, fostering community connections, and offering flexibility.
Career Growth and Learning Time
Cybersecurity professionals thrive when they see a clear path forward. To help them envision their future, lay out defined steps for advancement - like moving from a SOC Analyst role to becoming a Security Engineer or Architect . This kind of clarity can make all the difference in long-term retention.
Make learning part of the job. Schedule training sessions during work hours to show that skill-building is a core part of your strategy. Rob T. Lee, Chief AI Officer and Chief of Research at SANS Institute, explains:
"Training must be approached intentionally as a skills development strategy instead of a talent retention tool" .
Cover the costs of certifications and provide hands-on challenges to keep skills sharp. For example, earning a CISSP certification can boost salaries by 22% to 35% . Plus, 69% of hiring managers prefer candidates who’ve recently upskilled or obtained new certifications .
It’s also important to offer diverse career paths. Not everyone wants to move into management. Some may prefer diving deeper into technical roles like architecture or research. By providing multiple options, you ensure employees aren’t forced into leadership as their only way to grow . With 85% of employers prioritizing upskilling their current teams over hiring new talent , investing in internal development programs is a win-win. Mentorship programs can also be a game-changer, giving employees access to seasoned professionals who understand your company’s unique needs and culture .
And growth doesn’t stop at internal programs - it extends into broader industry engagement.
Conference Budgets and Community Participation
The cybersecurity world is a close-knit group, and staying connected is a big part of job satisfaction. 78% of cybersecurity professionals say the quality of their team is a major factor in their happiness at work . Help your team stay engaged by supporting their attendance at major conferences like DEF CON, Black Hat, and BSides. These events not only keep employees informed about the latest threats but also allow them to build meaningful relationships with their peers .
Offering an annual professional development stipend - anywhere from $5,000 to $10,000 - shows your commitment to their growth . Encourage participation in local OWASP chapters, regional BSides events, or other groups like SANS or ISSA. These connections help employees stay plugged into the larger cybersecurity ecosystem, which in turn strengthens your team’s collective expertise .
With 48% of security professionals feeling overwhelmed by the fast pace of new threats and technologies , community engagement can also help combat burnout. It’s a chance to recharge, learn, and bring fresh ideas back to your organization.
While professional development is crucial, flexible work options are another key factor in retaining top talent.
Flexible Work Options
Requiring full-time, on-site work is a dealbreaker for many cybersecurity professionals. The pandemic prompted a shift to remote work, and many in the field haven’t looked back. Remote-first roles are now a top priority for job seekers . The nature of cybersecurity work often makes it well-suited for remote execution .
Flexibility matters just as much as salary, especially for senior-level roles . With 45% of cybersecurity professionals citing high stress as a reason for leaving , offering remote or hybrid work options can help reduce burnout. Flexible schedules allow teams to recover after high-pressure incidents, which is critical for maintaining long-term productivity and morale . Being upfront about on-call duties and incident response expectations in job descriptions can also help build trust from the start .
Remote work policies don’t just benefit employees - they expand your talent pool. By opening up roles to international candidates, you can address local talent shortages . And if fully remote work isn’t practical, hybrid arrangements can still provide much-needed balance. Considering that 62% of cybersecurity leaders have experienced burnout at least once , flexibility isn’t just a perk - it’s a strategic move for retention and readiness.
Conclusion
Hiring cybersecurity engineers is far from your typical recruitment process. With a staggering 4.8 million unfilled positions worldwide, sticking to traditional methods won't cut it. Instead, you need a tailored strategy that aligns with the unique culture of security professionals and connects with them in their preferred spaces .
Start by clearly defining the roles you're hiring for. Whether it's a Security Analyst monitoring threats, an Engineer building robust defenses, or a Penetration Tester probing systems for weaknesses, each position requires a distinct skill set and appeals to different types of candidates . Getting specific about these roles ensures you're targeting your search effectively.
Next, focus on where these professionals spend their time. Use niche platforms like CTF (Capture The Flag) competitions, bug bounty leaderboards, or security-focused Discord communities to engage candidates in an environment they trust . Tools like daily.dev Recruiter can help you connect with engineers based on their reading habits and community activity. Forget cold outreach - warm, organic connections are far more effective.
Once you've made contact, prioritize practical skills over theoretical knowledge. Assess candidates with hands-on challenges like vulnerable code reviews, incident response scenarios, or threat modeling exercises rather than relying on trivia-based questions . This not only ensures you're hiring capable professionals but also reflects the unique demands of cybersecurity hiring. And remember: speed matters. The best candidates are often snapped up within 3–4 weeks, significantly faster than the typical 3–6 months for other roles .
But recruitment is just the beginning. To retain top talent, invest in their growth with career development opportunities, flexible work arrangements, and a supportive environment. With 88% of organizations reporting security incidents linked to skills shortages , building and retaining a strong security team isn't just important - it's non-negotiable.
FAQs
Which security role should I hire first?
Start with hiring a security engineer - this role is essential for building, implementing, and managing the core security systems your organization relies on. A security engineer helps establish a solid defense against ever-changing threats. Once you’ve got this foundation in place, consider adding specialized roles like penetration testers or SOC analysts, depending on your specific requirements. Taking this step-by-step approach not only strengthens your security measures but also helps navigate the challenges of the cybersecurity talent shortage.
How can I source security talent without LinkedIn?
If you're looking to recruit cybersecurity professionals, relying solely on LinkedIn might not cut it. The best talent often hangs out in specialized spaces tailored to their field. Here are some great alternatives:
- Bug bounty platforms like HackerOne and Bugcrowd are excellent places to spot skilled individuals actively solving real-world security challenges.
- Security conferences such as DEF CON and Black Hat offer opportunities to network with highly skilled professionals and gain insights into the latest security trends.
- Online communities on platforms like Slack or Discord often host security-focused groups where experts share knowledge and collaborate.
- Capture The Flag (CTF) competitions and research groups are treasure troves for finding candidates with hands-on experience and a proven track record in solving complex security problems.
These avenues are particularly useful when dealing with roles that require high levels of trust or security clearance, where traditional hiring methods might fall short.
What’s the best hands-on test for this role?
The most effective way to evaluate a cybersecurity engineer is through hands-on testing that measures their ability to identify and exploit vulnerabilities. Practical exercises should emphasize key skills such as code review for vulnerabilities, threat modeling, and incident response. Experience with platforms like HackTheBox or a proven track record in bug bounty programs can showcase their expertise in action. While certifications like OSCP can be valuable, they should complement - not replace - real-world skill assessments.



